The investigation into that matter is ongoing, and the company issued a video-based mea culpa to its customers, but unfortunately, the situation for the company just got worse. Here’s the basic timeline of events and where things stand so far:
• The first successful breach against Equifax occurred between May 2017 and July 29, when the intrusion was discovered.
• The secondary breach was just discovered this month, but actually occurred in March of 2017, before the main breach. The company maintains that the earlier attack had nothing to do with the most recent one, although a variety of anonymous sources claim that this is not the case.
• In both cases, Equifax retained the services of security company Mandiant to assist them with the investigation into the breaches
• As part of the company’s formal response to the breaches, they set up a website, “equifaxsecurity2017.com” which was designed as a portal that Equifax customers could use to see if they’ve been impacted by either breach.
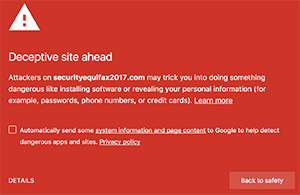
• Unfortunately, the company recently sent out a tweet to its customers directing them to “securityequifax2017.com” which is a phishing site, initially thought to be set up by the same hackers that attacked the company in the first place.
Equifax representatives quickly caught the mistake and deleted the tweet, but of course, the damage had already been done. As of today, Google Chrome now flags the phishing site as deceptive, but it is likely that at least some of Equifax’s customers clicked the link embedded in their tweet and found themselves on a bogus site.
The attack on Equifax, even considering the impact of the errant tweet, certainly wasn’t the largest hack we’ve seen in 2017 in terms of scope and scale. But it, taken together with the recent hack of the SEC’s EDGAR system, has done tremendous damage to the confidence in our economic system as a whole. Damage is done far beyond the physical size of the attacks and the total number of records impacted.It’s too soon to say whether this represents a trend, with hackers pursuing some type of agenda-based strategy in preference for simple theft, but recent events could very well be interpreted in that way. Time will tell.
In any case, the answer to the question asked in the headline is yes. For a brief time, Equifax did indeed direct its users via Twitter, to a bogus site.