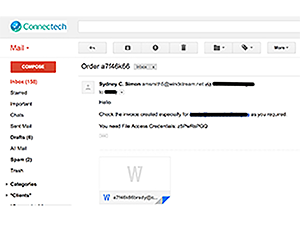
Red Flag! Phishing scams are still being used with naive internet device users who open up any attachment sent to them from unknown or untrusted sources. You may have received an email that looks quite legitimate from Sydney C. Simon of Windstream with a password protected MS Word invoice. You would think that individuals would stop and think twice before clicking or downloading such an invoice, but these hackers are relying on users who do not think and quickly click on the attachment and download it to their device. Very big mistake. This phishing scam is verified by Channel Partners. Windstream has an announcement of what to do if you receive any email purported to be from Windstream that you think is bogus. So what can you learn from this?
It is possible that this phishing or a similar scam is a Trojan that will download malware or ransomware and take over your device. Or it could be an attempt for you to enter sensitive or personal identity information where you shouldn’t. These types of nefarious internet/software downloads are sent as attachments in emails or text messages that trick an unwary and uninformed victim to click on and corrupt the device. The other type is tricking a naive victim to click on a link either in an email or on a website page that asks you for sensitive, personal identity information or downloads malware/ransomware to your device.
You should understand some basic concepts to protect yourself and any of your devices from these attacks whether you receive one from an email, text message, or on any web page you visit.What is a Trusted Source?
- Only download attachments, files, apps, files sharing software and plugins from trusted sources. Be especially cautious about free software offered online or via email (unsolicited attachments). Don’t click on anything until you think about it and verify it is a trusted source.
- Even if you receive an email, text message, or social networking from a trusted source, i.e., a known friend, your trusted source could have been hacked and the hacker is now using your trusted source to send nefarious scams to everyone in your trusted source’s contacts. It looks like your friend, but what has your friend sent you? Verify it is coming from your trusted source. For example, Yahoo was hacked and millions of accounts were compromised. Be wary of anything that entices you click on something to download. Instead of thinking twice, think three or four times before clicking on anything you download. The hacker is hoping you are trusting your friend to get you to click on something you shouldn’t. Be sure your trusted source actually sent you what you are clicking on. Verify your trusted source.
- Don’t use untrusted portable media, such as a stranger’s flash drive. If the flash drive is infected, it will infect your device.
- Never provide personal account information by email or text message, and use extreme caution when clicking links in messages or sharing information over the phone. Instead, visit the company’s website directly or call them yourself. If anyone is asking for personal information this should be a huge red flag to stop and think this over seriously before clicking or doing anything.
Trusted Web Sites
- Don’t click any link or button on a website without making sure that the address (URL) of the the company’s website appears to be correct. On your device, hover your pointer over the link to see the URL in the status bar. If you can’t see the status bar in your browser, find out how to display the status bar (taskbar) with your browser. On your iOS or Android device, touch and hold the link to view.
- If you’re not sure about the source of a browser pop-up window, avoid clicking any links or buttons in the window.
- Make sure the URL is secure. For more information on what this means read our post on this subject and Why Should Your Web Site Have SSL?
- When your browser WARNS you that you are downloading something that may not be from a trusted source this is your last warning.
Phone Call Scams
- Always confirm the caller’s identify before you provide any sensitive information over the phone. If you get an unsolicited call from someone claiming to be from a company you deal with, hang up and contact the company that called you directly to confirm the call.
Two Factor Authentication
- We have encouraged our clients to have two factor authentication to prevent hacking any device. This is the single best practice you can do to prevent a hacker from taking over your device. For a complete list of companies offering two factor authentication read our post on this subject.